Biometric Blitz: The Expanding Applications of Identification

The future is officially here – you can now buy a burger with your face.
Since 2017, International fast food chain Caliburger has been testing new, fully automated ordering kiosks that use facial recognition to remember customer’s payment information and order history, all with just a look. Such an advancement sounds astonishing, or even impossible, but Caliburger isn’t the first fast food enterprise to deploy facial recognition in their stores. In fact, that title goes to internet juggernaut Alibaba and their “smile to pay” service currently operating in Chinese KFCs.
Biometrics are on the rise, outside of law enforcement and spy thrillers. VISA’s biometric pilot program aims to embed paper-thin fingerprint scanners into debit cards for an added layer of financial security, while IrisID’s iris scanners are currently being used to track employee hours in the sugar mills of El Salvador. Biometrics are everywhere, from airports and hospitals to shopping malls and daycares, and understanding their inner workings, and their applications, is the key to understanding the future of identification.

What Are Biometrics?
The term “biometrics” doesn’t refer to a singular technology or trend, but rather the many ways a person can be physically measured. A fingerprint, for example, is considered a mode of biometric identification, but so is height, gait, and even typing rhythm. Almost every aspect of our physiology, including our behavioral patterns, can be measured and analyzed. However, qualifying as a biometric measure that doesn’t automatically guarantee a reliable form of authentication.
Height and weight are incredibly imprecise biometric categories. Millions of people stand at 5’7, so knowing a person’s height won’t necessarily single them out from a crowd. Meanwhile, fingerprints are so unique not even identical twins have matching prints.
The popular use of the word “biometrics” tends to refer to the later, narrower category of identification. Fingerprints, faces, irises, palm veins, and retinas are usually what comes to mind when discussing biometrics, and for good reason. Such features are incredibly distinctive and easier to quantifiably compare, allowing for quick and secure identification.
Generally speaking, when you hear the word “biometrics” in the news, it’s referring to these unique, comparable markers of identity.
How Does Biometric Analysis Work?
The short answer: with a lot of math.
The less short answer: with a lot of math based on analyzing patterns.
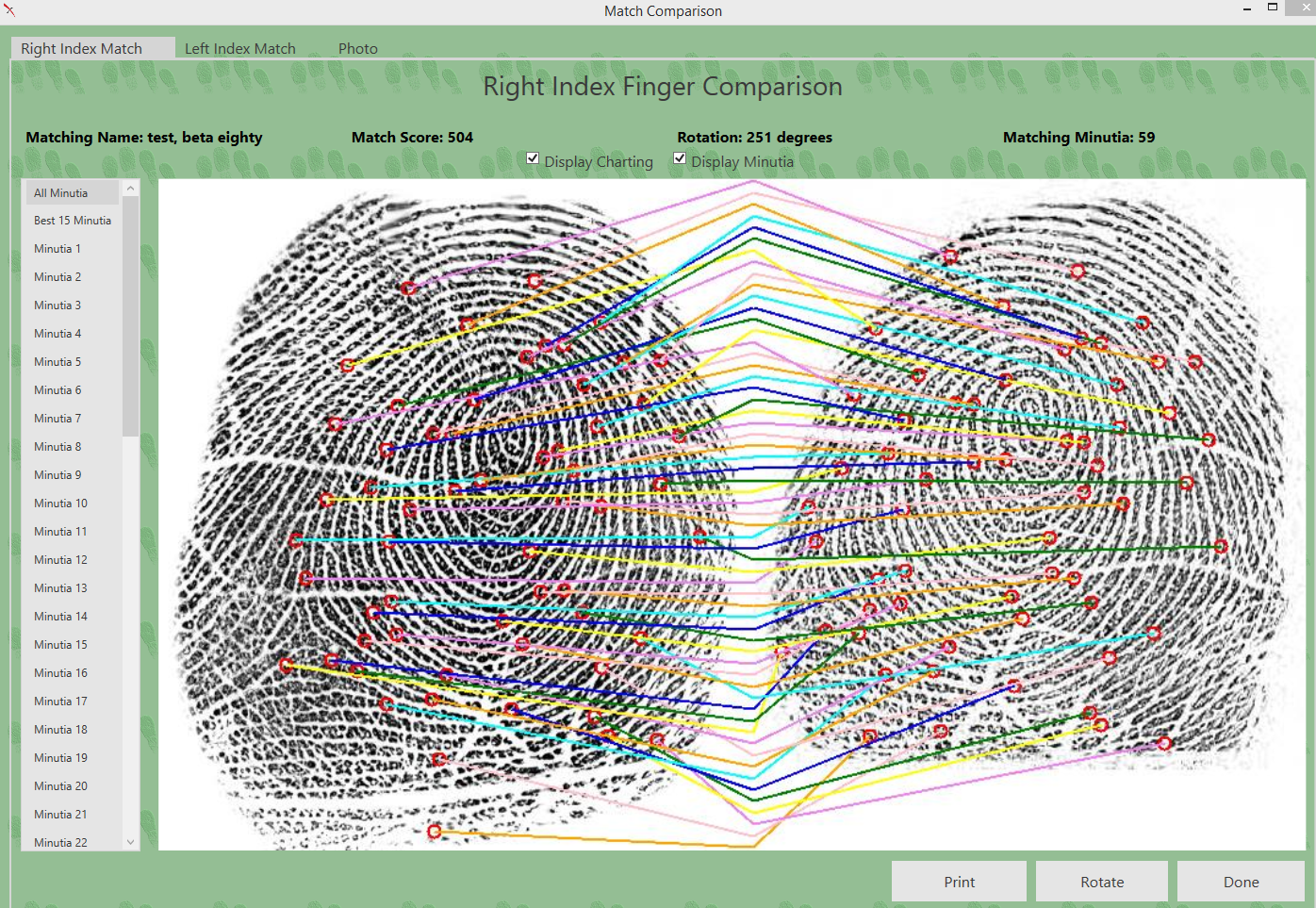
At its core, biometrics is about comparison. About matching minutes details from one print to the next. For irises this involves texture and depth, for fingerprints its about ridges and curves. Either way, the goal is to create an intricate, mathematical map of a face, finger, or eye that can be used as a point of comparison for another biometric map. The more closely one captured fingerprint matches another, the stronger the likelihood that those captures are of the same finger (and therefore person).
How in-depth a biometrics analysis goes depends mostly on application. A smart phone’s capacitive fingerprint sensor, for instance, isn’t held to as rigorous a standard as an FBI certified criminal fingerprint scanner. Similarly, the threshold for a “match” can be raised and lowered depending on need.
On the hardware end, there are dozens of ways to capture biometric data. Live scanners use high definition scanners to image fingerprints rolled over a thick glass platen, while iris recognition systems use near-infrared cameras to photograph the unique patterns in the eye. Biometric capture technology varies from solution to solution, but it all comes back to patterns and points of comparisons. Typically, a biometric system will center around an imaging system (usually a camera), and some form of matching algorithm. The packaging, however, can vary.
If you’re interested in the specific ways biometric data can be captured and cataloged, the FBI has been spearheading new methods of identification since the launch of their Next Generation Identification (NGI) initiative. You can read more about NGI here.
A Brief History of Biometrics
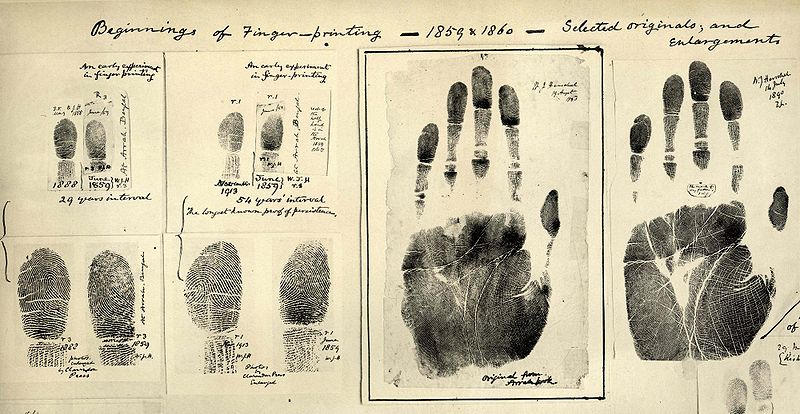
Contrary to popular belief, facial recognition and fingerprinting are hardly new. Even before the days of cameras and live scans, humans have been keen on finding new and clever ways to objectively determine who is who.
Before Juan Vucetich pioneered fingerprinting in law enforcement in 1891, forensic anthropometry (the act of taking numerous, detailed measurements of the body such as the arms, legs, and skull) was the de facto method of identification. While it may seem crude now, these measurements were surprisingly thorough, and unique enough to be useful for correctional facilities around the world. Of course, taking and filing an upward of ten measurements per person, including wrist circumference and finger length, gets very tedious very quickly, and such anthropometric methods fell by the wayside once fingerprinting came into prominence.
But biometrics didn’t stop with inked fingerprinting. As early as 1964 Woodrow Bledsoe used computers to begin analyzing mugshots in a preliminary attempt to develop facial recognition software. A few decades later in 1989, fingerprinting went paperless with the advent of live scanning. The first iris scanning algorithms, developed by John Daugman, debuted in 1991, and by 1999 the FBI launched its first computerized system for sorting, comparing, and exchanging fingerprint data.
In 2013 – a mere fourteen years after the FBI’s first digital fingerprint archive – Apple marked a major turning point in consumer electronics by introducing capacitive fingerprint recognition technology into their smartphones, a development that quickly caught on in mobile phones the world over.
Now, in 2018, Windows 10 Hello uses IR cameras to let you sign into your windows devices in seconds.
To say biometrics has grown in leaps and bounds over the past fifty years would be an understatement.

The Benefits of Biometrics
The most obvious draw toward biometrics is security, and for good reason. Most of our tried and true methods of identification haven’t aged well since the dawn of the internet. Social Security Numbers (which once bore a “NOT FOR IDENTIFICATION” label) are incredibly easy to steal and store en masse, leading to regular data breaches and leaks like the infamous Equifax affair. Documents like birth certificates and drivers’ licenses are a little harder to forge outright, but with the advent of cheap printing and anonymous cryptocurrency, getting your hands on a forgery is easier than ever. In fact, it’s so easy that over 30% of underaged college sophomores have successfully used a fake ID to purchase alcohol.
As technology advances and it becomes easier and easier for unsavory elements to gain access to your personal information, biometric authentication remains the only form of identification that can’t be lost, stolen, or otherwise forged. Fingerprints are forever, and literally always within arm’s reach. They can’t be guessed like a password, or cracked like an encrypted file, and though it makes for good TV, they can’t be easily forged with silicone molds or disembodied (yikes!) fingers.
Biometrics are also quicker and more convenient than traditional identification, and in the case of facial recognition and iris scanning, they can be entirely touch free. Iris capture in particular takes a fraction of a second, and cuts down on fumbling with cards or punching in pin numbers. In places that require clean facilities, such as research labs and hospitals, this is a major advantage over traditional security. Even school cafeterias could benefit from a touch free payment system, especially come flu season.
Being able to restrict access to secure locations and precisely monitor traffic throughout a building are vital for places like hospitals and schools, where the wrong person in the wrong place can prove dangerous. Unlike keycards, which can be lifted from pockets or drawers, or passwords that require frequent changes and memorization, with biometric authorization it’s possible to control exactly who walks into, and out of, your doors.
There are also obvious law enforcement applications. The growth of national fingerprint databases has already lead to breaks in decades-old cold cases across the country, putting violent criminals behind bars and bringing justice to their victims. As our biometric knowledge grows, so do our opportunities to solve the unsolvable with detailed latent print analysis and facial recognition software.
Identification and Privacy
Much has been said about the intersection of biometric identification and personal privacy. While biometrics are secure and convenient, there’s something very intimate, or even unsettling, about the idea of our fingers and faces winding up in some nameless government database.
Public opinion has largely shifted in the past decade, fully embracing biometric authentication and its growing applications. But while the majority of consumers are comfortable with using their prints to pay for their coffee, doubt still lingers about our privacy in the age of the internet.
However, a lot of fear and discomfort comes from misunderstanding. Not all biometric databases are alike, and the kind of scanning and submission used in correctional facilities bears little resemblance to civilian systems. Many local archives, like the kinds used to identify employees or students, have no connections to any governmental databases, and therefore never submit enrollee information to outside entities. The kinds of identification solutions used in office buildings and consumer electronics are small, closed systems that treat fingerprints and iris scans like keys, rather than like records. Your smartphone doesn’t submit your fingerprints to the FBI every time you unlock it, instead it remembers the prints you’ve previously enrolled, then checks each finger against that small group of prints.
Where your biometric information goes, and how it is used, depends entirely on context.
But those nameless government databases (sans biometrics) do exist, and they’re filled with intricate details about every facet of our lives. From voting records to tax returns, our information has always been collected and cataloged for the sake of administration and identification. The only difference is how usable that data is to someone who isn’t you. Writing down another person’s SSN when opening a bank account is easy, providing another person’s finger print…not so much.

Applying Biometrics
While it is true that biometrics are the cornerstone of modern law enforcement and criminal processing, that only scratches the surface of what secure identification can do.
There are few industries that wouldn’t benefit from an added layer of security and convenience. Being able to pay for fried chicken with a smile makes for a great headline, but there are other more practical applications of biometric identification. The TSA PreCheck integrated Clear Program uses iris and fingerprint scanning to dramatically reduce security wait times in airports across the country. In Pinellas County Florida, students use palm vein scanners to pay for their lunch in an instant, instead of punching in a long, easy to mistype pin number.
There’s also the Brevillier retirement community in Eerie, Pennsylvania. Brevillier employs iris scanning at each exit to prevent residents with cognitive impairments from walking out the door and into very real danger, while also allowing its unimpaired members to come and go as they please.
Facial recognition has thwarted tens of thousands of cases of fraud in New York, stopping thousands of drivers with revoked licenses (usually due to multiple DWI convictions) from getting behind the wheel. Facial recognition has also been deployed in the Yahama concept bike MOTORiD to allow the motorcycle to recognize its owner, which is less important than stopping crime but is pretty cool regardless.
Anywhere a card, password, key or pin is used, biometrics can be used more securely, and more efficiently, instead.
When it comes to the future of biometrics, burgers are just the beginning. If you or your agency is interested in expanding your biometric systems beyond traditional live scanning, contact us at info@mentalix.com.
